Services > Data and Privacy Protection
Data and Privacy Protection
Organizations today face increasing challenges protecting their most valuable data and sensitive information. From dealing with a variety of file formats to safeguarding the movement of data, it is more important than ever to have a comprehensive approach to information protection in place to ensure that all data has appropriate levels of confidentiality, integrity and availability.
Breach of Data Can Be Catastrophic
Loss or breach of data can be devastating to a business or organization. The impact can be calculated in many ways, from hard dollar costs and business downtime to repercussions associated with the premature disclosure of sensitive data such as layoffs or financial results.
As unstructured data grows, so do enterprise risks
Exponential growth in unstructured data volume, expanding data protection regulations, and the proliferation of on-premises and cloud storage options makes securing the organization’s unstructured data nearly impossible today.
Evolving privacy regulations require companies to identify, manage, and secure unstructured data from unauthorized disclosure. The main problem customers face is large volumes of data with no index of the risk.
Securing Your Data
Edgile can help you protect and manage your data regardless of where the data resides, how it’s being accessed or who is using it. Our solutions empower knowledge workers by giving you the tools and training necessary to protect the unstructured business data you create and manage. Instead of addressing a single element, our data protection strategy employs a comprehensive approach that looks at the entire solution, including persistent data protection, data loss prevention and incident response.
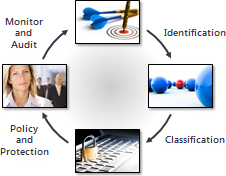
Edgile architects, designs and deploys solutions to automate the identification, classification, access controls and auditing of usage for your most sensitive information. Our approach ensures that you have the processes, standards and training to give knowledge workers real-time data when and where they need it, while preventing unauthorized use of digital information.
Learn about public key infrastructure (PKI) related services
More from Edgile experts
Optimizing Microsoft 365 control settings for reduced risk in the cloud
As a trusted Microsoft Gold security partner, Edgile has developed four detailed Microsoft 365 Configuration Guides offering pre-engineered control settings for Microsoft…
Continue Reading Optimizing Microsoft 365 control settings for reduced risk in the cloud
The importance of Identity and Access as enterprises shift to the cloud
Business operations are becoming more complex as the number and type of users increases, coupled with their ability to access a growing…
Continue Reading The importance of Identity and Access as enterprises shift to the cloud
Assessing and managing cloud security risks
Edgile’s Office 365 Configuration Guides identify a comprehensive set of control requirements with inherent and residual risk ratings for Office 365/EM+S E3…
Continue Reading Assessing and managing cloud security risks