Services › Data & OT/IoT Security
SERVICENOW ELITE PARTNER
Data & OT/IoT Security

Our Offerings
Data Security
The convergence of Information Technology (IT) and Operational Technology (OT) in the Industry 4.0 transformation is revolutionizing the modern business landscape. By harnessing the power of cutting-edge technologies businesses are achieving growth, increased productivity, and enhanced customer experiences. These advancements pose security challenges that organizations must address.
Data Discovery & Classification
Secure sensitive data against internal and external threats, integrate dark data and transform unknown data into valuable business assets.
Insider Threat Protection- DLP, CASB, IRM, DAM
Enhance data security posture by proactively safeguarding against potential internal threats and unauthorized access.
Encryption and Cryptographic Services
Strengthen data integrity, confidentiality, and resilience against cyber threats for data at rest, data in motion and data in use.
Data Access Governance
Ensure secure and compliant access to information, safeguarding sensitive data and minimizing risk.
Ransomware Protection
Achieve Cyber Resiliency against data extortion, enabling quick recovery and minimizing potential data loss threats.
Trust as a Service
End-to-end data protection across the rest, transit, and in use phase with confidential computing that provide secure and trusted execution environments for applications.
OT/IoT Security
The integration of Information Technology (IT) and Operational Technology (OT) in the Industry 4.0 transformation is revolutionizing the modern business landscape. By harnessing the power of OT for efficient and effective operations and incorporating cutting-edge technologies, businesses are experiencing growth, enhanced productivity, and improved customer experiences. However, these advancements also pose security challenges that organizations must address.
OT/IoT Risk Assessment and Advisory Consulting
Enable to meet the security compliance requirements and define roadmap for OT/IoT Cyber security.
Threat & Vulnerability Management
Provide visibility within OT/IoT network for threats, communication and vulnerability identification.
Secure Remote Access
Let 3rd party connect to your network securely.
Network Segmentation
Isolate and protect critical assets from external threats.
OT/IoT SOC and Managed security services
Respond faster and efficiently to cyber threats.
Secure your edge-to-cloud journey against the evolving cyber threat landscape with a Zero Trust approach.
Wipro offers the best global cloud and infrastructure security solutions, technology, AI-powered sustainable automation platforms and highly-skilled talent—Cybersecurists—to accelerate growth that is both secure and optimized for cost efficiency.
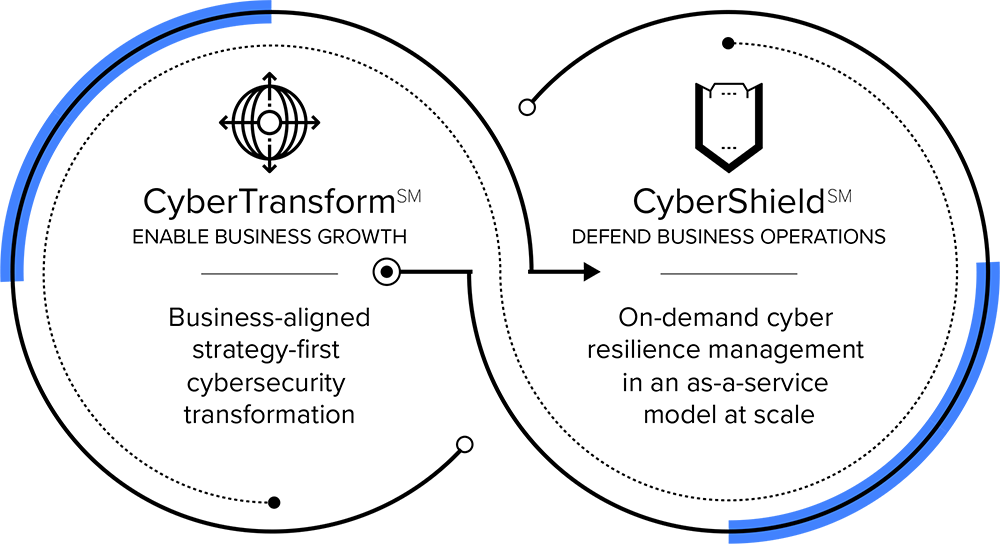
We offer a modern end-to-end framework for cloud and infrastructure security transformation — CyberTransformSM – that includes advisory and implementation, plus our industry-leading managed services — CyberShieldSM. Our recent acquisitions and key investments in this area have created additional value for our customers across the globe.

Partners















Connect with Edgile to get started
For details on how to optimize your risk and security programs, please contact your Edgile representative.
























