MODERN IDENTITY SOLUTIONS
Physical Access + Identity Management
Integrated SailPoint connector for Lenel OnGuard badge management

Automate and manage your physical access systems
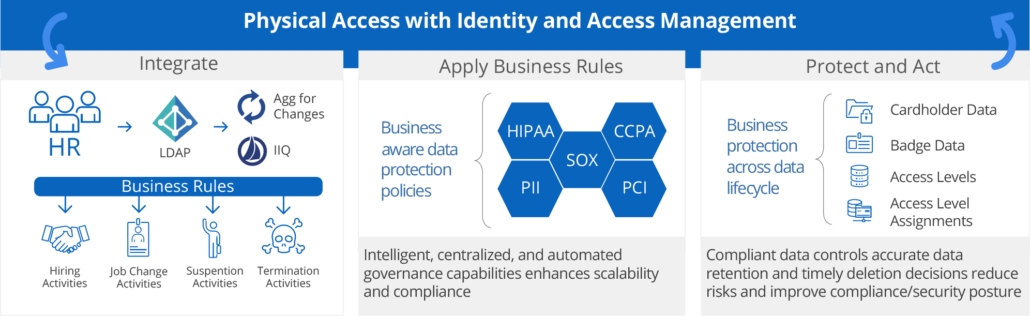
Organizations need their physical access management to be married to their Identity and Access Management (IAM) system, to allow seamless access to secure locations for employees with the proper access authority.
This is challenging because badge management technology hasn’t kept up with modern IAM, resulting in problems—too much access, too little access or untimely access assignment.
Edgile has developed a modern solution. Our comprehensive read and write SailPoint connector for Lenel OnGuard allows organizations to fully leverage SailPoint’s best-in-class IdentityIQ and IdentityNow products to automate and manage physical access.
Edgile’s Badge Management Methodology
Edgile’s inclusive processes drive data protection sustainibility
Edgile helps you build, execute, or fix your physical access management strategy
Physical access management integration journeys are unique to each organization. Over time, changing strategies, directions, priorities and technologies can disrupt the best laid plans. Integrations can range from more simplistic, like certifying access level assignments, to more robust, like full management and self-service integration of badge functionality, depending on your organization’s priorities, use cases and requirements.
Edgile offers three service levels to help you achieve your badge management goals.
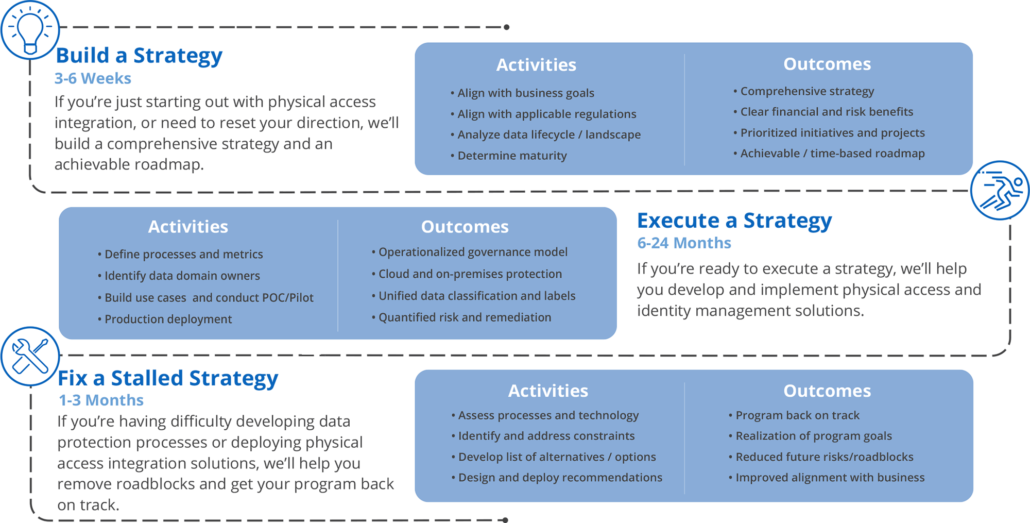
Build Strategy
3-6 Weeks
If you’re just starting out with physical access integration, or need to reset your direction, we’ll build a comprehensive strategy and an achievable roadmap.
Activities
- Align with business goals
- Align with applicable regulations
- Analyze data lifecycle / landscape
- Determine maturity
Outcomes
- Comprehensive strategy
- Clear financial and risk benefits
- Prioritized initiatives and projects
- Achievable / time-based roadmap
Execute a Strategy
6-24 Months
If you’re ready to execute a strategy, we’ll help you develop and implement physical access and identity management solutions.
Activities
- Define processes and metrics
- Identify data domain owners
- Build use cases and conductPOC/Pilot
- Production deployment
Outcomes
- Operationalized governance model
- Cloud and on-premises protection
- Unified data classification and labels
- Quantified risk and remediation
Fix a Stalled Strategy
1-3 Months
If you’re having difficulty developing data protection processes or deploying physical access integration solutions, we’ll help you remove roadblocks and get your program back on track.
Activities
- Assess processes and technology
- Identify and address constraints
- Develop list of alternatives / options
- Design and deploy recommendations
Outcomes
- Program back on track
- Realization of program goals
- Reduced future risks/roadblocks
- Improved alignment with business
Connect with Edgile to get started
For details on how we can help formalize your Physical Access Management strategy, please contact our ldentity Team.