Services › ServiceNow Risk and Security › ServiceNow Security Operations (SecOps)
The modern Security Operations challenge
Security Operations (SecOps) and incident response teams work hard at keeping businesses safe from ever-evolving threats while supporting new digital transformation initiatives. Every second counts in this environment, but often IT security programs are hampered by siloed teams, manual processes and disconnected tools and datasets. They can get bogged down with the repetitive tasks of collecting, sorting, and analyzing threat data.
As cyber threats become more advanced, SecOps programs must transition to proactive, automated and integrated solutions.
Automate your security tools and run seamlessly with IT
Edgile’s diagnostics engagements and Quick Start implementation packages use a “reporting first” approach, leveraging the built-in SecOps capabilities in ServiceNow.
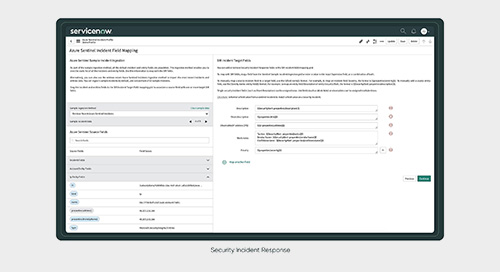
ServiceNow SecOps brings incident data from your security tools into a structured response engine that uses intelligent workflows, automation, and a deep connection with IT to prioritize and resolve threats based on the impact they pose to your organization.
We help you demonstrate to management, risk, compliance, and audit stakeholders that your SecOps capabilities are effectively meeting threat intelligence objectives and actively reducing risks from security incident and vulnerability responses.
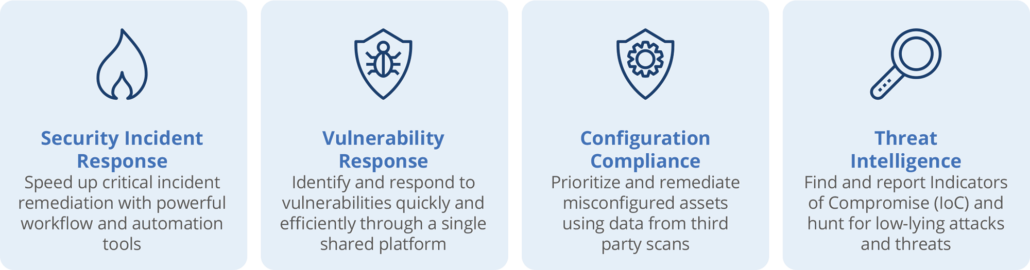
Scale security solutions to specific threat responses
ServiceNow SecOps applications allow you to scale your security solution to meet your business needs and respond to the specific cyber threats you face.
View On-Demand Edgile Demos
SecOps OVERVIEW
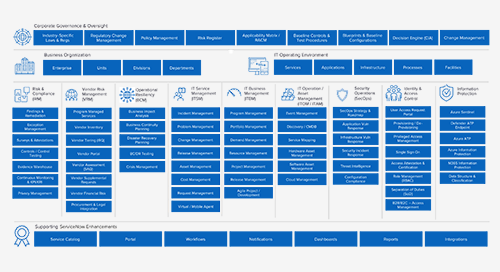
EDGILE RISK AND SECURITY SOLUTIONS





ServiceNow Security Operations (SecOps) Resources
Prepare Your Operational Resiliency For Changing Rules and Evolving Threats
Shocks to supply chains, the emergence of hybrid work environments, and rising cyber security risks are reconfiguring the world. In this environment,…
More Prepare Your Operational Resiliency For Changing Rules and Evolving Threats
ServiceNow Delivers New Security Integrations with Microsoft to Help Organizations Stay Protected and Resilient in the Hybrid Era of Work
By Brian Rizman and David Deckter Today at Knowledge ’21, ServiceNow announced a strategic Security Operations‑focused integration with Microsoft that extends the partnership…
Respond Faster with ServiceNow Security Operations and MITRE ATT&CK Framework
Learn how other organizations are extracting greater value from their existing ServiceNow Security Operations investments by incorporating the MITRE ATT&CK evaluation results…
More Respond Faster with ServiceNow Security Operations and MITRE ATT&CK Framework
ServiceNow Security Operations (SecOps)
SecOps teams work hard at keeping organizations safe from ever-evolving threats while supporting new digital transformation initiatives. But often, IT security programs…
Edgile Named Elite Partner by ServiceNow
Delivering IRM, VRM, BCM, SecOps and Regulatory Compliance solutions and providing clients 20+ ServiceNow Industry Apps AUSTIN, Texas, January 28, 2021 — Edgile, the…
Why a Risk Register Helps a CISO Communicate to the Board [11:46]
In this latest edition of An Insider’s Look At Security and Compliance hosted by Evan Schuman, Edgile’s Brian Rizman explains that in…
More Why a Risk Register Helps a CISO Communicate to the Board [11:46]
Connect with Edgile to get started
For details on how to optimize your risk and security programs, please contact your Edgile representative.